Role: Cloud Security Analyst Consultant - Amdari.io
Domain: Cloud Security, Identity & Access Management (IAM), Cloud Governance
Duration: 07, March 2026 - 27, March 2026
Tech stack & tools: Microsoft Azure (Subscriptions, Resource Groups, Virtual Machines), Microsoft Entra ID (Azure AD), Azure RBAC, Azure Portal (GUI), Microsoft Graph PowerShell module, Azure CLI, Microsoft Authenticator.
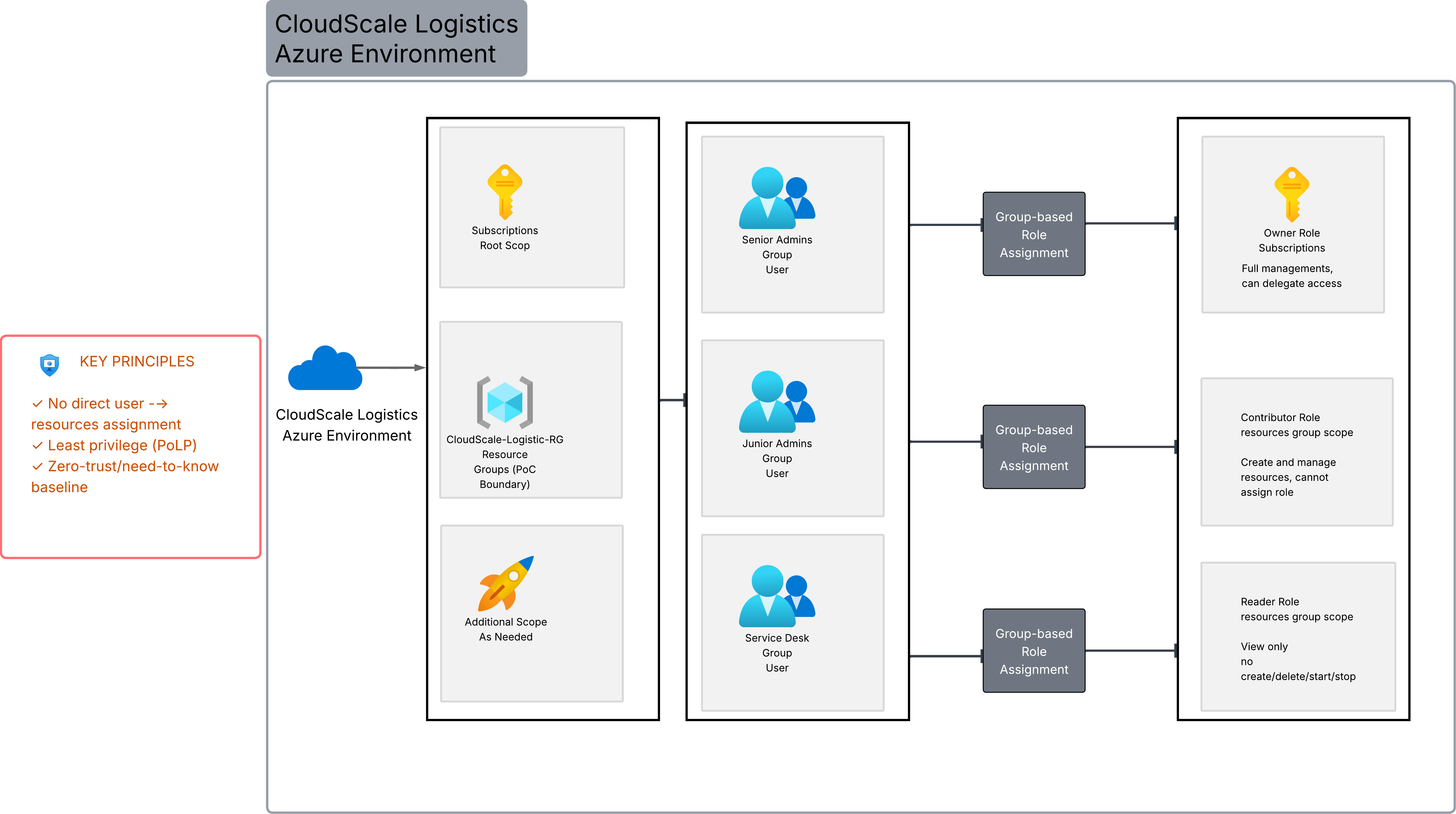
Project overview: CloudScale Logistics is a mid-sized global shipping and supply chain provider rapidly expanding its workloads into a multi-subscription Azure environment. As the environment grew, the team relied on manual, user-level permission assignments, which led to permission creep, an unnecessarily large attack surface, and growing compliance risk. As a Cloud Security Analyst Consultant at Amdari.io, I designed and implemented a group-based RBAC model in Microsoft Entra ID and Azure to enforce least privilege, establish a zero-trust, need-to-know baseline, and create a repeatable identity and access pattern.
Context and problem: The IT team lacked a standardized access hierarchy across Azure subscriptions, and permissions were granted directly to individual user accounts on resources. Over time, this created a situation where many users, including Service Desk personnel, accumulated high-privilege roles such as Owner that exceeded their daily operational duties. This model made it difficult to answer basic security and compliance questions such as who has what access and why, increased the blast radius of any single compromised account, and made onboarding new administrators slow and manual.
Objectives:
- Eliminate direct user-to-resource role assignments and move to a group-based RBAC model in Microsoft Entra ID.
- Establish a zero-trust, need-to-know baseline where identities can authenticate but have no default access to Azure resources.
- Design a tiered administrative model for Senior Admin, Junior Admin, and Service Desk roles mapped to Azure RBAC roles: Owner, Contributor, and Reader.
- Ensure access can be managed consistently through Azure Portal, Microsoft Graph PowerShell, and Azure CLI.
- Reduce administrator onboarding time from several hours of manual assignments to a single group membership change.
- Improve audit readiness and support cleaner access reviews for standards such as SOC 2 and ISO 27001.
Architecture and access design: To isolate the proof-of-concept and enforce regional data residency, I created a dedicated resource group named CloudScale-Logistics-RG in the East US region. This resource group served as the management boundary for deploying test resources and validating role behavior without impacting production workloads. I then designed a three-tier administrative structure that mapped Microsoft Entra ID security groups to Azure RBAC roles at clearly defined scopes: Senior Admins to Owner at subscription scope, Junior Admins to Contributor at resource-group scope, and Service Desk to Reader at resource-group scope. All access was assigned to groups instead of individual users, removing direct user-to-resource assignments and enforcing least privilege.
Implementation:
- Used Azure Portal to manually create the initial Senior Admin identity, representing the highest administrative tier and following governance-friendly naming and profile practices.
- Used Microsoft Graph PowerShell to automate Junior Admin provisioning by installing the Graph module, connecting with the required scopes, creating user accounts and the Junior Admins security group, and adding users to the group with commands such as
Connect-MgGraph, New-MgUser, New-MgGroup, and New-MgGroupMember.
- Used Azure CLI to provision Service Desk identities, create the Service Desk group, add members, and support broader role-assignment and resource-management workflows.
- Audited existing role assignments with Azure CLI to identify direct user permissions and excessive Owner access, including Service Desk users holding privileges beyond their responsibilities.
- Migrated access from direct user assignments to group-based RBAC and verified effective assignments using Azure CLI role-assignment queries.
Validating zero-trust and least privilege: I tested both authentication and authorization across all three tiers. All users were confirmed in the tenant and validated for sign-in and MFA registration using Microsoft Authenticator. After deploying a test virtual machine, I confirmed that Owner users could create, modify, and delete resources, Contributor users could manage resources but not assign roles or change access control, and Reader users could view resources and properties but could not create, delete, or start and stop the VM. Attempted actions beyond Reader scope correctly resulted in access denied behavior, demonstrating blast radius limitation.
Cost management and decommissioning: To avoid unnecessary spend and leave the environment clean, I listed resources with Azure CLI, deleted proof-of-concept resources, removed the CloudScale-Logistics-RG resource group, and verified that no unnecessary cost remained after decommissioning.
Results:
- Reduced administrator onboarding time from several hours of manual per-resource assignments to a single group membership change, typically under five minutes.
- Eliminated direct Owner role assignments for non-admin identities such as Service Desk, significantly reducing the attack surface.
- Confirmed that Reader-level accounts could not perform destructive or state-changing actions on Azure resources, limiting blast radius.
- Established a reusable, group-based RBAC pattern aligned with least privilege and zero-trust principles.
- Improved audit readiness by centralizing role assignments on Entra ID groups, simplifying periodic access reviews for SOC 2 and ISO 27001.
- Demonstrated cross-platform IAM management via Azure Portal, Microsoft Graph PowerShell, and Azure CLI, increasing operational flexibility.
Challenges and learnings: This project deepened my understanding of Azure RBAC scopes and inheritance across subscriptions and resource groups, and showed how balancing usability with strict least privilege is central to effective cloud governance. It also highlighted how Azure Portal, Microsoft Graph PowerShell, and Azure CLI complement each other when building reliable and auditable IAM workflows.